Use a password manager
Use a password manager. It is more convenient, more secure, and enables a better workflow for enabling healthy cyber security.
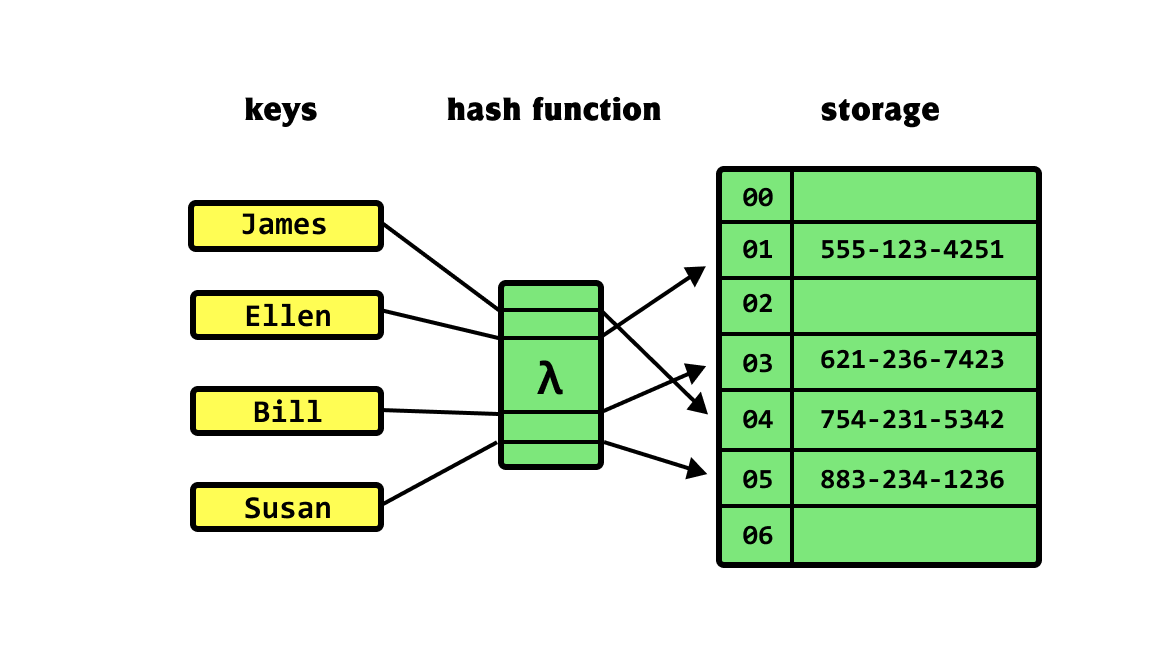
First, let me tackle the importance of the security benefits of a password manager to those who aren’t concerned about attacks from nation-state level actors. Part of the modern paradigm of online personal security is accepting that even the best protected and most advanced companies get breached, a lot (LinkedIn, Dropbox, Evernote, Blizzard, etc etc.) Ideally those companies/sites will be following up-to-date protocols and won’t store your passwords directly. Instead they will store a “hash” of your password.
Simply put, a hash of some data is a unique representation of the original data from which it is very difficult to get back the original data.
 Hash functions, courtesy of Wikipedia
Hash functions, courtesy of Wikipedia
To test if you’ve entered the correct password, the site will hash your input and compare the hash to the one they have stored for you.
Hash(<user inputted password>) ?= Hash(<your password>)
When a company gets breached and leaks your data, they will hopefully only leak this hash and not the passwords themselves. Unfortunately with modern compute power all that is required to go from hash -> password is computing the hash of every possible password. Here is a table of the number of calculations required to check every password of a certain type:
| Time to crack (@10M hashes/second) | ||
|---|---|---|
| Password Type | Compute seconds | Compute years |
| 4 lowercase only | 0.05 | 0.00 |
| 4 all characters | 6.56 | 0.00 |
| 8 lowercase only | 20,882.71 | 0.00 |
| 10 lowercase only | 14,116,709.57 | 0.45 |
| 10 all characters | 3,486,784,401,000.00 | 110,565.21 |
Summary: short non-complex passwords are useless. Often following a breach hackers will crowdsource the process to reverse the hashing and within a few days all easy passwords will be cracked. At this point it is common for people to attempt the email/username + cracked password combination on various other sites hoping that the target uses the combination commonly. Often the process would be automated for a few sites thought to be valuable (for example: Facebook, Twitter, Amazon, Bank of America, Capital One) and then any accounts from the original leak with matching credentials to any other valuable sites on the internet will also be compromised. Generally these accounts are sold in bulk for less than $10/account.
The point is:even if you believe that your data is uninteresting it is unlikely that hackers would target you, the process of breaking credentials in bulk and selling them is not personalized: it is automated and done en-mass. Eventually the credentials are used by some less sophisticated criminal who learned to use the darkweb and bought them for the equivalent of a pack of ramen and wants to try to use your Amazon to send him weightloss pills for his fat wife in Russia.
 Your hacker (Image)
Your hacker (Image)
How does a password manager fix this?
The reason most people don’t use complex passwords is due to the inconvenience. Those who do use complex passwords tend to share them across all of their accounts because they can’t be bothered to memorize their 24-character long string of random nonsense more than once. To have a secure online presence your passwords need to be:
- Unique to each site
- Complex and long
- Switched with regularity
A password manager allows you to have unique passwords for every site that look like #K2wtnmnghS#0VZZ8b6frYh6$ at minimal added inconvenience. When you want to replace: generate a new one, store it in your manager and forget it again.
As for what password manager to use, there are very many. You can do your own research if you wish (they all have 90% of features in common and only basic functionality is required), but I can only recommend the one I use as a result of being grandfathered in over the years: LastPass.
The primary way you would interact with LastPass is through their Chrome extension. If you don’t use Chrome, start using Chrome.
You can try to use your built-in Google password safe or iCloud keychain, but I primarily use MacOS + Linux + Chrome + iOS so the workflows for a platform specific password manager are not perfect.
Summary: Use a password manager, it is worth the 10 minutes required to set it up.
